Securing Access via ODBC using Enforcive
With ODBC it is very easy for users to download data from an IBMi database to their PC's bypassing green screen security. If a user has access to a file via a native IBMi application written in a native IBMi language, then they have the ability to download that data to their PC, if there is no exit point security in place.
Now that more and more people are accessing systems remotely, it is important to create more layers of security to protect your vital data. Indeed GDPR legislates that IT departments implement this type of security.
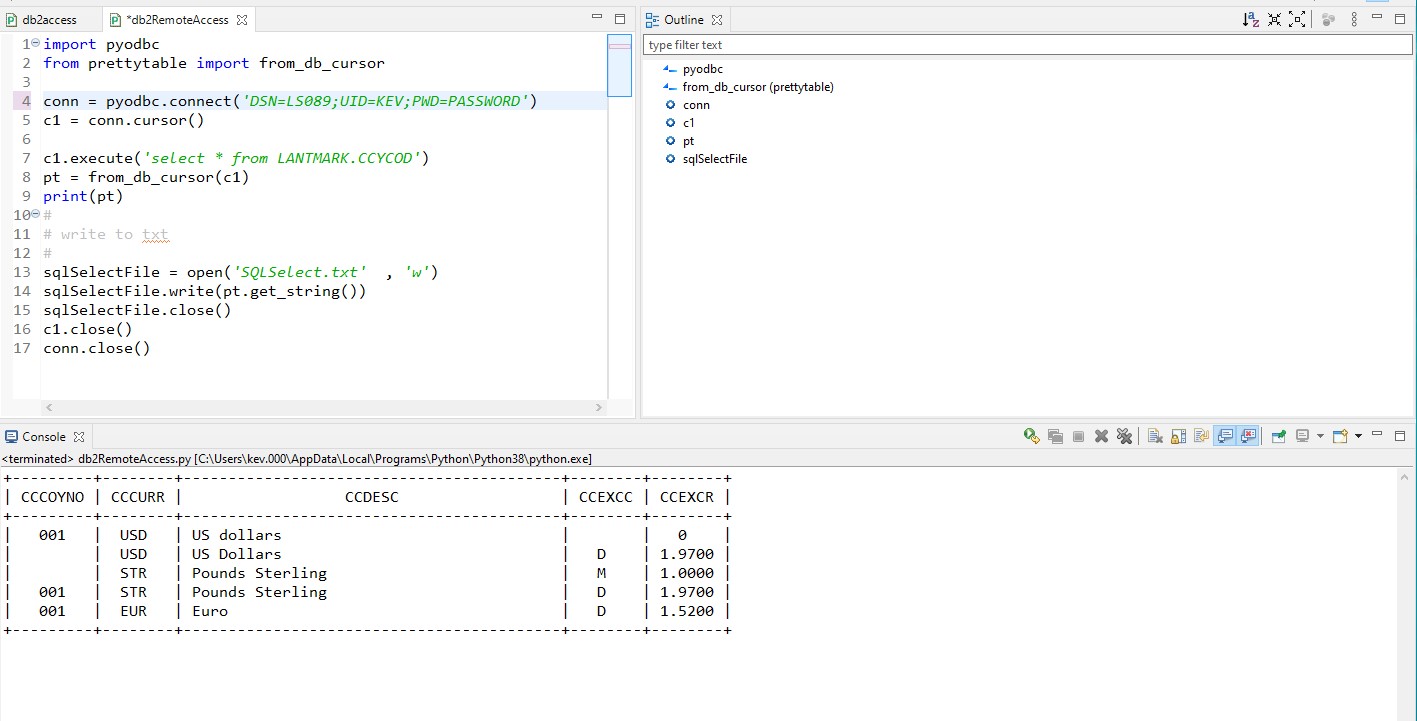
Using an ODBC connection, data can be downloaded in less than a dozen lines of code.
Here is an example:-
This small python script connects to an IBMi database and the SQL select statement pulls the entire file from the database, the results are shown below. The last three lines before the close statements create a remote text file(it could easily be a spreadsheet) from the data extracted.

Without any exit point security you would not be able to monitor or protect your system from this type of interaction with your database on the IBMi.
Enforcive's Enterprise Security Application easily protects your data with a couple of clicks..
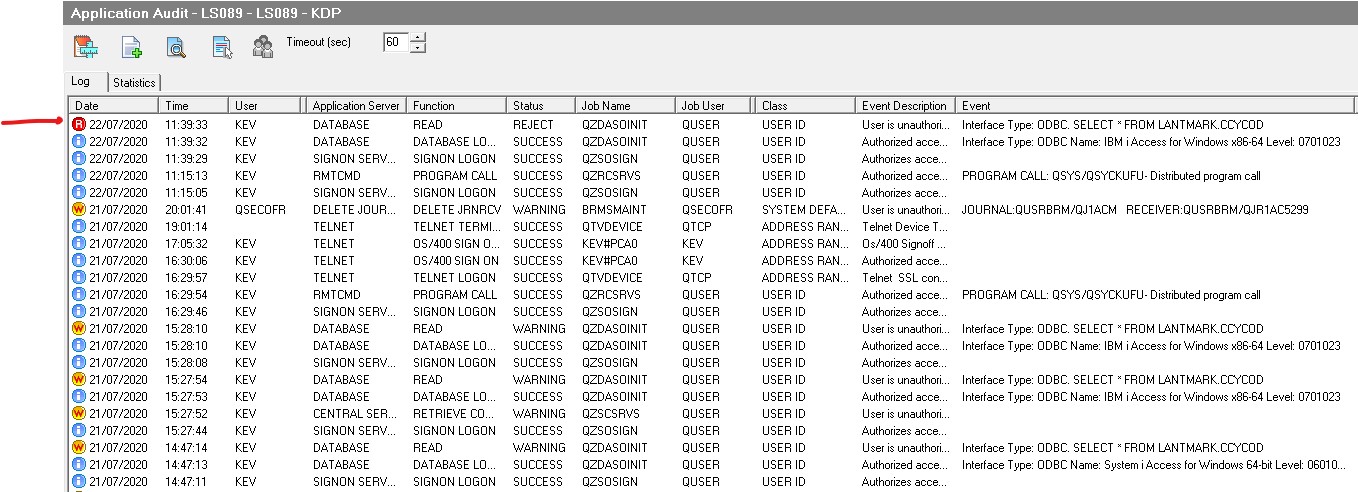
Using the application Audit Module the security team can easily spot access via ODBC.
Here is a look at what is logged.
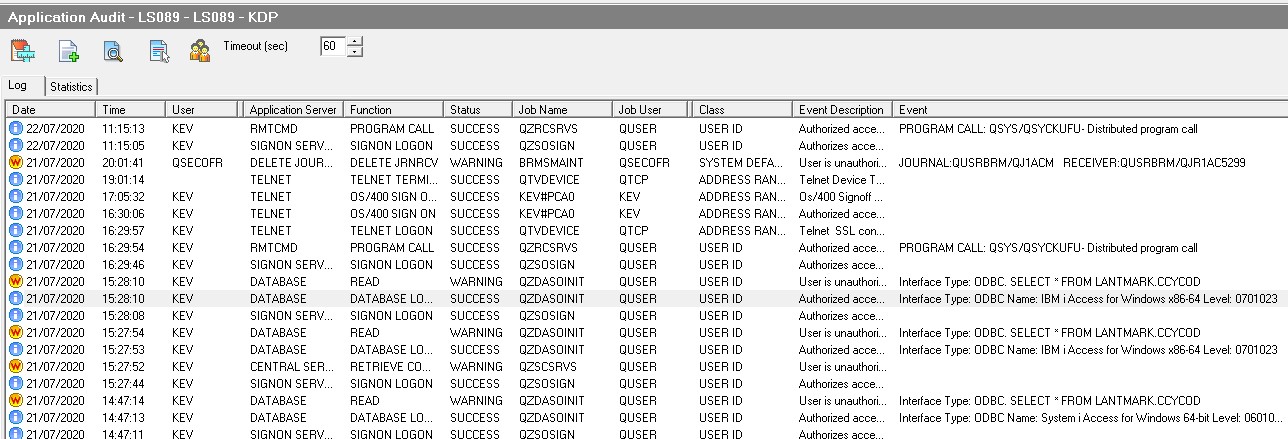

The highlighted line shows the database logon and details how the user logged on and with which interface. The statement prior shows what information was extracted.
At the moment Enforcive is in monitoring mode and the warning indicates that this access is against the policy I have created, however the access has been allowed.
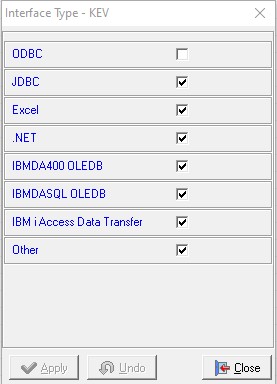
To stop this access requires that I place this particular interface in "Reject mode".
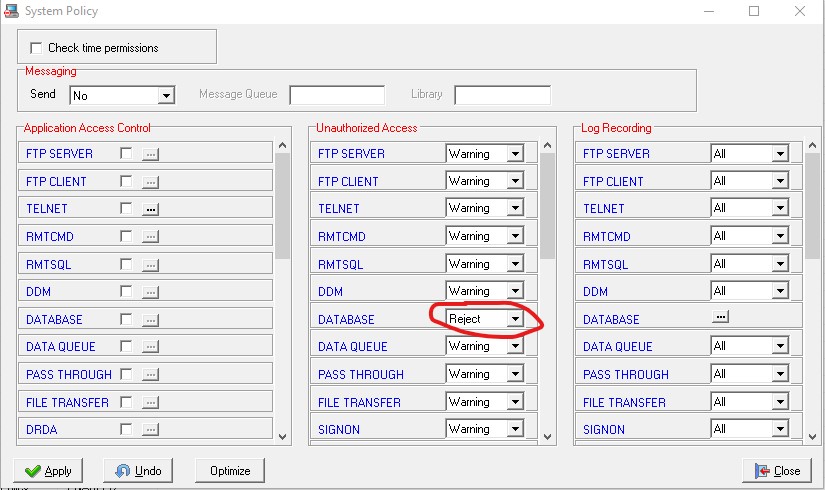

Now my database is protected.

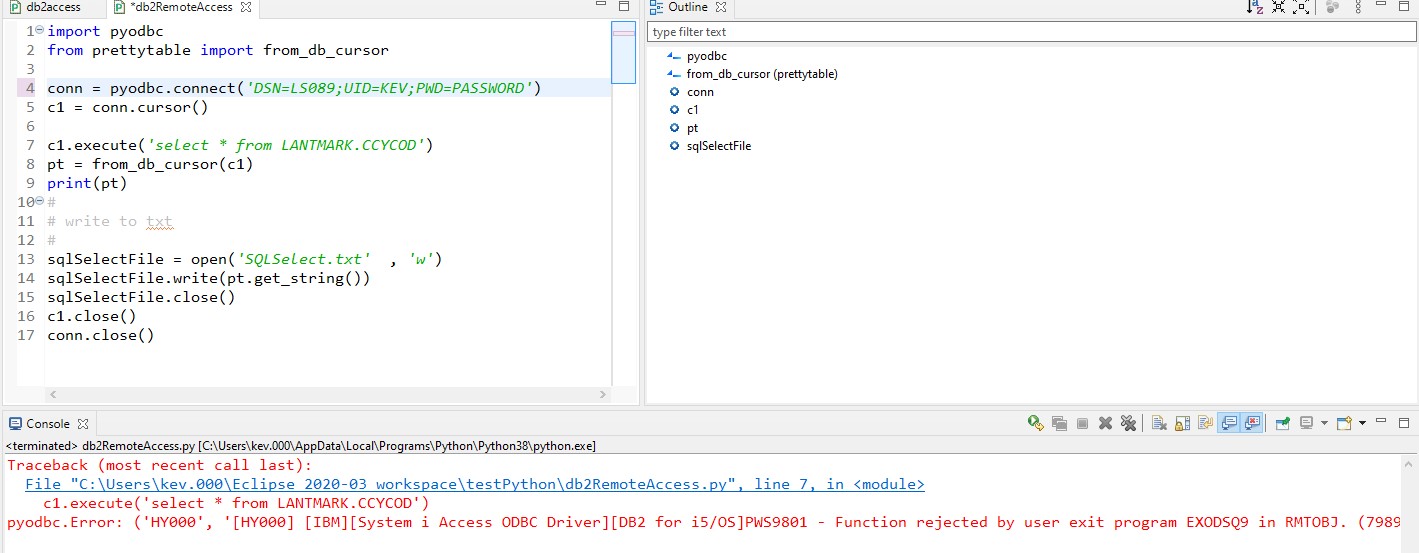
Here is what Enforcive logs.

I can also reject access to the database logon by unselecting the ODBC logon parameter and deny access to the signon server.
Here are the interfaces I now allow:-

And the resulting Application audit.

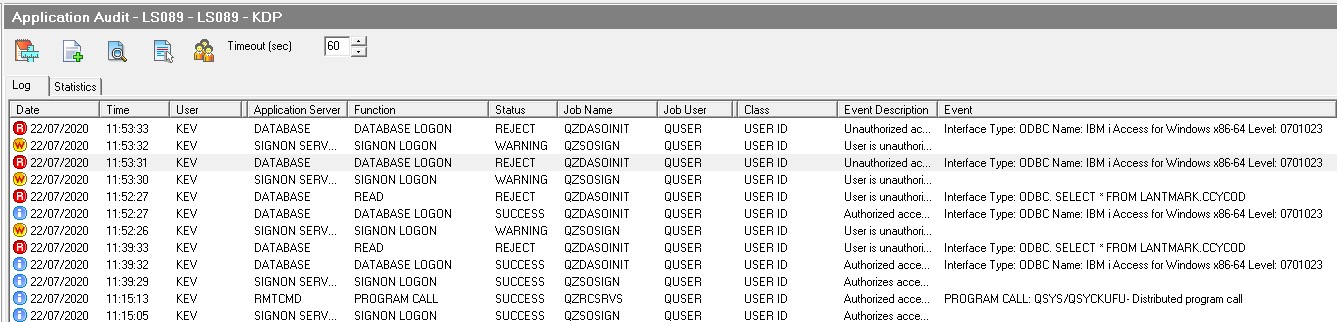
My signon server is in warning mode only - hence the warning. The great thing with this is that you can monitor your system for a while and when you have your policies in place and working you can then set your server to "Reject" mode without interrupting legitimate access.



